Palm Beach’s New Playbook: Blending Privacy, Resilience, and Cyber-Physical Security
Palm Beach stands at a rare intersection. Private banks and family offices continue to expand along Royal Palm Way and Rosemary Square. Port and utility operators manage assets sitting feet from surge zones and salt air. The county’s growth brings new capital and new digital risk.
The coastline adds storm pressure and cyber-physical exposure. One operating model can strengthen both: pair the privacy controls expected by affluent clients with the resilience practices needed for waterfront systems. The result is fewer losses, faster recovery, and a stronger brand for “Wall Street South.”
Finance Inflows and Higher Privacy Expectations
Palm Beach’s financial footprint continues to grow. JPMorgan opened a financial center on Royal Palm Way and announced a second West Palm Beach office at 360 Rosemary. These moves support a rising population of affluent clients now living and working here year-round.
New tenants at One Flagler and nearby towers, including Bessemer Trust, Paulson Capital, HighPost Capital, and multiple family offices, expand the region’s attack surface through cloud tools, vendors, and payment workflows.
With this growth comes rising privacy expectations. Family offices want clear controls for wires, document sharing, and account changes. Payment verification steps can prevent business email compromise, a top risk in private transactions.
Local cases highlight the stakes. Boynton Beach Police recently recovered over $100,000 after an email scam targeted a business owner. Wire fraud remains the most common threat in private deals and construction draws. The fundamentals still matter: break payment workflows into verifiable steps, keep changes off email, and lock down vendor portals.
The 2019 Riviera Beach Shock Still Guides Planning
Palm Beach County still remembers the 2019 Riviera Beach ransomware incident. Malware crippled city systems, taking down phone and email lines and forcing dispatchers to write 911 calls by hand. The city ultimately authorized a ransom of nearly $600,000.
The incident pushed cyber risk to the front page for local leaders. Its lessons still apply:
Segment networks
Test backups and restoration times
Maintain a crisis playbook spanning tech, finance, and communications
Align cyber insurance and legal review before an incident
Palm Beach Port: Island Economies & Cyber-Physical Discipline
The Port of Palm Beach is more than a local employer. It is a lifeline for Caribbean trade and a supplier for the Bahamas, with historic outbound cargo levels approaching 80% and a record 2.8 million tons in 2024. Fuel, food, sugar, and construction materials move through tight windows and constrained berths.
An outage hits revenue, and in some cases, island shelves. Cyber-physical risk grows as terminal systems, access control, and vessel services connect to enterprise networks. Operators need role-based access, continuous monitoring, and strong separation between operational technology (OT) and IT environments.
Federal regulators shape this picture as well. In July 2025, the Coast Guard established a temporary security zone covering portions of Lake Worth Lagoon, the Intracoastal, and adjacent Atlantic waters. Zones like these reinforce a simple truth: physical controls and information controls must move together.
A phishing email with remote access can disrupt dispatch, gate, or fueling systems. A bridge closure can slow incident response if staging plans aren’t ready.
Storm Planning: Cyber Impact and Data Recovery
Palm Beach County completed a Climate Vulnerability Assessment in 2024 and continues to build its Resilience Action Plan. The South Florida Water Management District updates its Sea Level Rise and Flood Resiliency Plan annually, with 2025 workshops emphasizing county-to-county coordination.
Statewide resilience programs guide funding for pumps, gates, drainage, and shoreline assets. Cyber leaders should translate these physical assets into network diagrams, backup plans, and recovery timelines. The same map that directs flood crews can direct tabletop exercises for data loss and power degradation.
From Flood Maps to SOC Playbooks
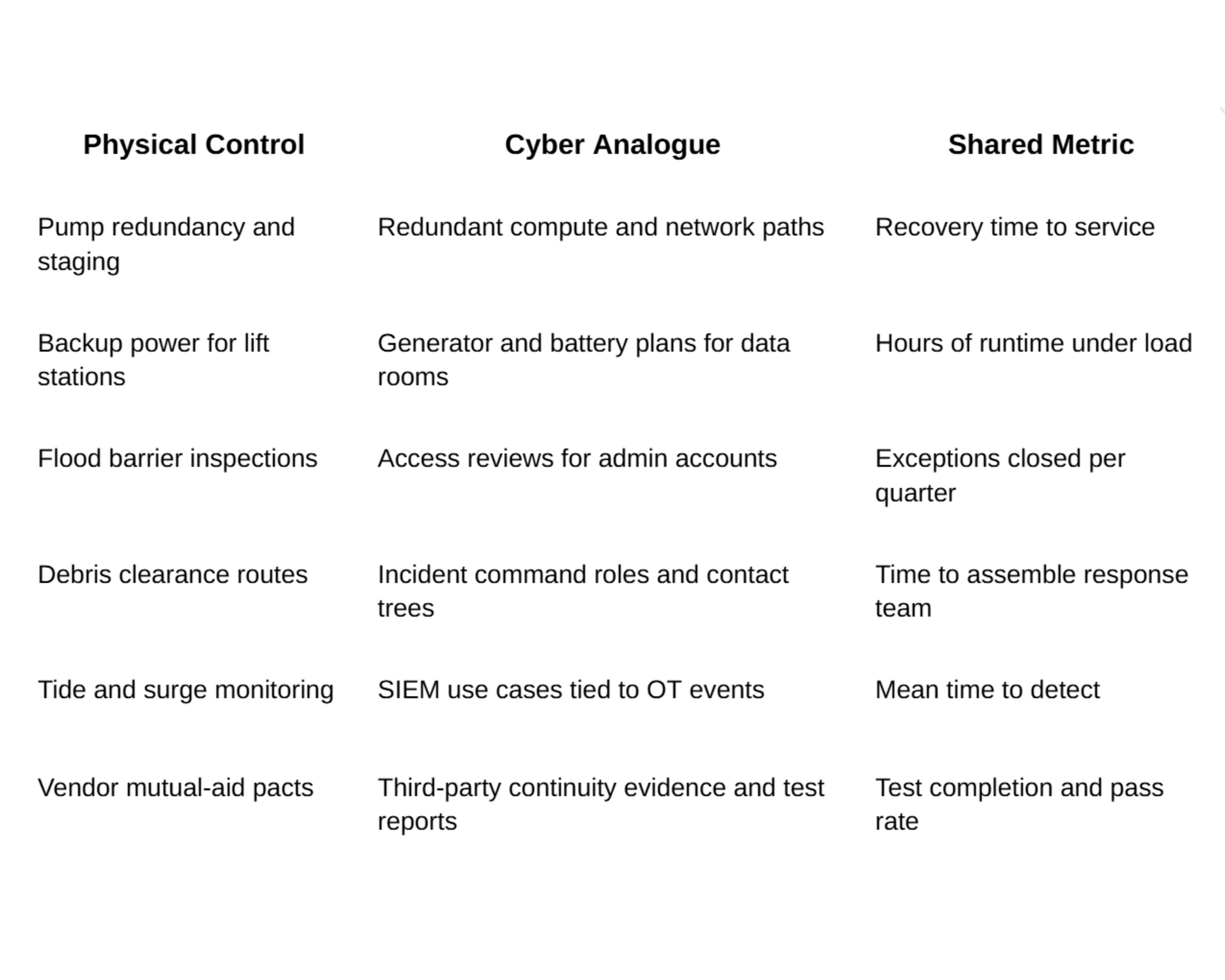
Physical resilience and cyber resilience share a common language: critical assets, dependencies, and time to recover.
Alignment guide:
Risk teams can turn this table into a scorecard. County resilience initiatives and SFWMD plans supply the inputs, while state programs help boards justify joint cyber-physical investments.
Talent Pipelines and Local Partners
Workforce matters as much as tooling. Florida Atlantic University provides cybersecurity pathways across its Business, Engineering & Computer Science, and Science colleges, covering security operations, risk, analytics, and policy. Companies can link internships to incident testing or vendor risk.
Regional business groups and the Business Development Board highlight innovation assets such as Boca Raton Innovation Campus (BRiC), where healthtech and software firms operate on a single campus. These networks help leaders source talent and shared services without flying in every role.
Payment Controls for Private Wealth & Real Estate Deals
Palm Beach continues to attract high-net-worth families, executives, and major real estate and marine transactions. Payment fraud follows that activity.
Local law enforcement reports show frequent intervention in wire scams, with partial recoveries when banks act quickly. Firms can harden controls without adding friction:
Use dual approval for account changes
Confirm changes through a known phone number
Avoid links and attachments in email confirmations
Use positive pay and name-match checks for large disbursements
These steps stop most fraud attempts before funds leave the county.
Vendor Risk that Reaches the Waterline
Third-party platforms power everything from portfolio reporting to port gate scheduling. Many promise continuous monitoring, but fewer can prove it.
Boards should ask for:
Service maps identifying single points of failure
Regional failover details, not generic cloud claims
Test reports covering degraded power, telecom outages, and water intrusion
County and SFWMD resilience documents provide realistic scenarios that can be embedded directly into vendor contracts and testing.
Case Note for Port and Utility Operators
Operators can borrow tactics from private banks. Email security prevents invoice fraud targeting maintenance crews and marine vendors. Access reviews remove dormant accounts on crane systems and SCADA equipment.
Accurate asset inventories help determine what to power down during a surge and what must stay online with generator support. Port cargo trends shift annually, and recovery plans should match those shifts. A record tonnage year increases the cost of downtime and raises the bar for incident drills.
A Shared Quarterly Test Cadence
Cross-sector drills build muscle memory. Run one tabletop per quarter that brings private banks, city staff, and waterfront operators together in West Palm Beach.
Keep the scripts local:
A late-season storm knocks out part of the telecom ring
A construction-draw email fraud attempt unfolds mid-incident
Two vendors drop out to simulate supply-chain failure
The session ends with a finance review linking the event to cash flow and insurance
The output: named people, time targets, access routes, and communication plans across bridges and security zones.
Buyer’s Guide for Palm Beach Leaders
Replace long checklists with focused sub-plans that teams can own and measure.
Payment and client protection:
Verified call-backs for all payment changes
Out-of-band final authorization
Daily reviews for high-value disbursements
Track losses and near-misses at the board level
Incident testing with weather and power injects:
Blend cyber events with storm impacts
Plan for cellular congestion and flooded access roads
Test generator logistics and fuel contracts
Record time to assemble and restore
OT segmentation and access control:
Separate IT and OT networks
Use jump hosts and session recording
Rotate credentials after contractor work
Review remote-access logs after every storm watch
Third-party continuity with local hazards:
Require tests that include surge, salt intrusion, and extended outages
Demand named failover sites and recovery-point targets
Link renewals to test completion
Use state and district resilience plans to shape scenarios
What to Do in the Next 90 Days
Run a cross-sector tabletop blending a wire-fraud attempt, telecom degradation, and a bridge closure. Produce a one-page roster of roles and phone numbers.
Complete a vendor continuity audit for core platforms across banking, payments, terminals, and access control. Map failover evidence to critical services and flood zones.
Turn the alignment table into a scorecard with FAU support. Use it at the board level and refresh quarterly. The result is a countywide playbook that treats privacy and resilience as one discipline.